DeFi Best Practices for Q2 2026: Security, Due Diligence, and Risk Management
DeFi Best Practices for Q2 2026
DeFi has changed significantly over the past year. The ecosystem has matured, threats have evolved, and the tools and infrastructure available to users look very different from what existed even 12 months ago.
For anyone participating in DeFi in Q2 2026, whether a newcomer exploring yield opportunities or an experienced user managing a diversified portfolio, keeping up with evolving best practices has become essential to protecting capital and getting the most out of what the space offers.
This guide covers the practical habits, tools, and frameworks that experienced DeFi users are applying in 2026. It focuses on security, due diligence, risk management, and the operational hygiene that separates users who preserve capital from those who don't.
Wallet Security: The Foundation
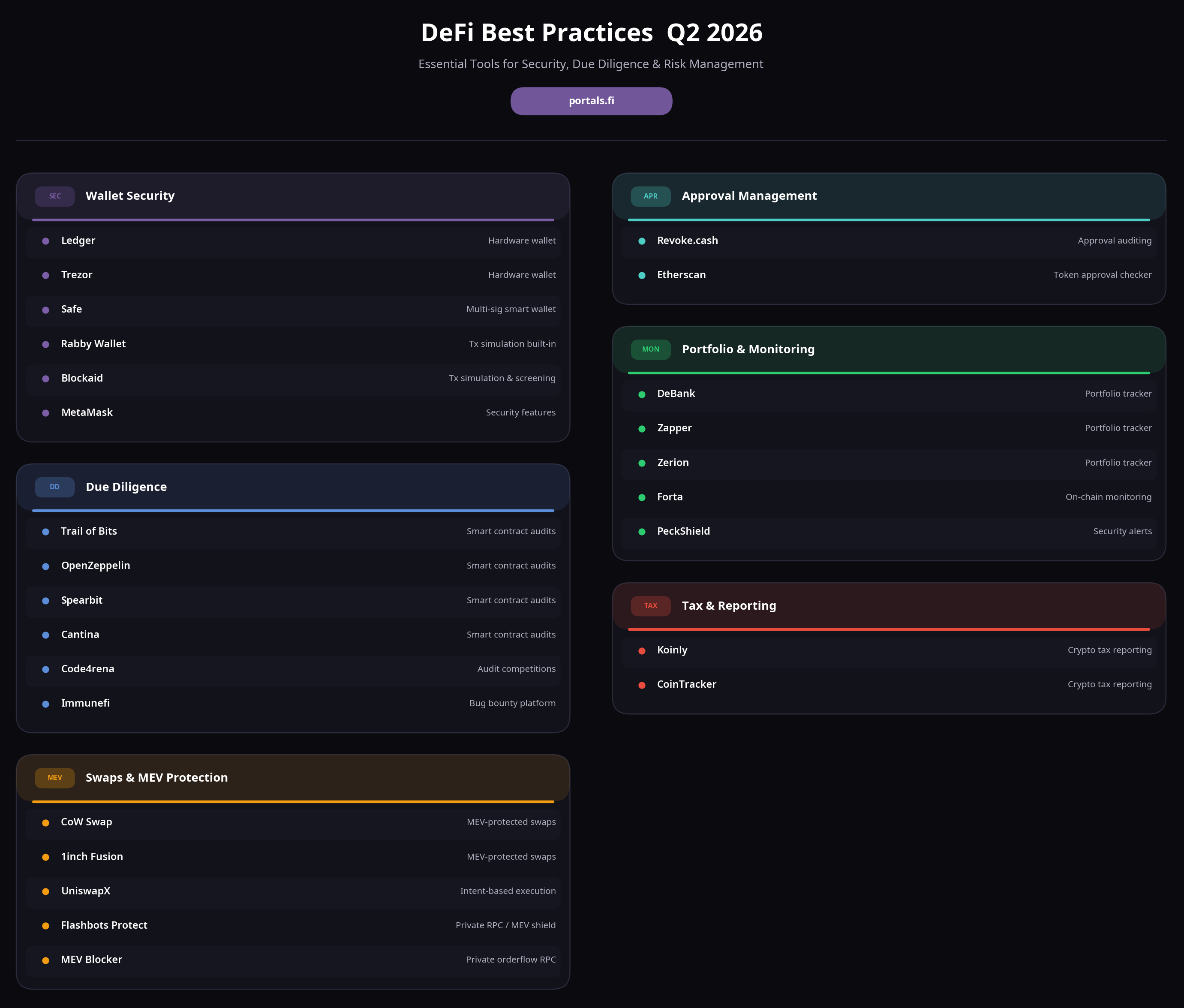
Wallet security remains the single most important area of DeFi best practice, and the threats have grown more sophisticated. Hardware wallets continue to be the gold standard for holding significant value. Models like Ledger and Trezor store private keys in secure elements that never expose them to the internet, meaning even a fully compromised computer cannot drain funds without physical access to the device and its PIN.
The shift toward smart contract wallets has accelerated through 2025 and into 2026, with account abstraction (ERC-4337 on Ethereum) enabling features like social recovery, spending limits, and session keys. Smart wallets from providers like Safe (formerly Gnosis Safe), Argent, and newer entrants offer meaningful improvements in both security and usability compared to traditional externally owned accounts. Multi-signature setups, where multiple devices or parties must approve transactions, remain the best practice for treasury-sized holdings.
Transaction simulation has become standard practice. Tools like Blockaid, Rabby Wallet's built-in simulation, and MetaMask's security features preview what a transaction will actually do before signing. This catches the majority of phishing attempts and malicious approvals before they can drain funds. Every DeFi user should be using a wallet or extension that provides transaction simulation by default.
Approval Management
Token approvals, permissions granted to smart contracts to move tokens on your behalf, are one of the most overlooked risk areas in DeFi. Many exploits in 2024 and 2025 succeeded not by stealing private keys but by exploiting old, unlimited token approvals that users had granted to protocols years earlier.
Best practice is to audit approvals regularly using tools like Revoke.cash or Etherscan's token approval checker. Unused approvals should be revoked, and when possible, users should grant specific amounts rather than unlimited approvals. Some newer protocols and wallet interfaces automatically suggest limited approvals for routine swaps, which significantly reduces the attack surface.
Approval risk compounds across chains. Users active on multiple networks should audit approvals on each chain they use, as a compromised approval on any chain creates a drain risk for tokens on that specific chain. Dedicated dashboards that show cross-chain approvals in one view have become standard tools for active DeFi users.
Due Diligence on Protocols
Not all DeFi protocols are created equal, and the quality gap has widened as the ecosystem has matured. Before depositing capital into any protocol, users should understand the basic questions: Has the protocol been audited, and by which firms? How long has it been live? What is the total value locked, and is that TVL stable or driven by recent incentive programmes? Who are the team and the investors behind it?
Audit quality matters more than audit quantity. Leading firms like Trail of Bits, OpenZeppelin, Spearbit, Cantina, and Code4rena provide rigorous review, while lower-quality auditors can create false confidence. Checking whether a protocol has a bug bounty programme on Immunefi or similar platforms provides an additional signal of security maturity.
Oracle design is a subtle but critical factor. Protocols that use spot prices from single DEXs as oracle inputs have historically been vulnerable to flash loan price manipulation. Protocols using robust oracles with TWAPs, multi-venue aggregation, and circuit breakers are significantly more resistant to the attack patterns that have drained hundreds of millions of dollars from DeFi over the years.
Governance structure is increasingly relevant. Protocols with active, decentralised governance that ships real changes tend to adapt better to new threats. Protocols with captured or inactive governance often fall behind on security practices. Reviewing recent governance proposals and voter turnout gives a quick read on whether a protocol is alive and responsive.
Risk Management and Position Sizing
Diversification remains fundamental. Concentrating on a single protocol, regardless of how secure it appears, exposes users to specific smart contract risk that no amount of diligence can fully eliminate. A practical heuristic used by many experienced DeFi users is to limit exposure to any single protocol to a percentage of total DeFi allocation that reflects the user's confidence in that protocol's security (often 5-20% for even well-established protocols).
Chain diversification matters as well. Concentrating on a single chain exposes users to chain-level risks, bridge failures, sequencer outages, and regulatory actions. Spreading across major networks (Ethereum mainnet, Arbitrum, Base, exceed, and other production L2s) reduces exposure to single-chain events.
Yield that significantly exceed comparable protocols' yields warrants additional scrutiny. Unusually high APYs typically reflect unusually high risk (either explicit, like leveraged strategies, or implicit, like poorly audited code or unsustainable emissions). The historical pattern is that the protocols offering the highest unsustainable yields have produced the largest losses when they eventually fail.
Position sizing should account for liquidation risk when using collateralised borrowing. Keeping collateralisation ratios well above minimum thresholds provides buffer against sudden price movements. Users should actively monitor positions and set up alerts for price movements that approach their liquidation thresholds, rather than relying on hope.
Staying Current on Threats
The DeFi threat landscape evolves rapidly. Information sources that experienced users rely on include on-chain monitoring services (like Forta and PeckShield alerts), security-focused Twitter/X accounts and researchers, and protocol-specific Discord or Telegram channels where issues get discussed in real time.
Phishing attacks have become far more sophisticated in 2025 and 2026. Sophisticated phishing sites now replicate DEX interfaces pixel-perfect, use compromised or lookalike domain names, and inject fraudulent transaction requests into legitimate-looking user flows. Bookmarking official protocol URLs, using the official app directly (rather than clicking links from social media or emails), and verifying domain names before signing transactions all significantly reduce phishing exposure.
Discord and Telegram compromises remain frequent attack vectors. Scammers regularly compromise or spoof official protocol channels to post fraudulent links. Users should treat any link in a Discord or Telegram channel as untrusted and verify the destination URL before connecting their wallet or signing anything.
New Threats in 2026
AI-assisted phishing and impersonation have become a significant concern in 2026. Attackers use LLM (large language models) to craft personalised phishing messages, deepfake video calls to impersonate team members or contacts, and automated social engineering campaigns that adapt to target responses.
The defences are largely the same as before, verify identity through known channels, never sign transactions based on unsolicited requests, use hardware wallet confirmations, but the sophistication of attacks has increased meaningfully.
Cross-chain bridge exploits remain a top source of large losses. While bridge security has improved significantly, bridges continue to be among the highest-value targets in crypto. Users should minimise time spent holding assets on bridges, prefer bridges with the strongest security models (canonical rollup bridges, native asset bridges with robust validation), and be cautious about bridges offering unusually fast or cheap transfers.
Sequencer risk on Layer 2s is a relatively new concern as L2 usage has grown. Most production L2s still use centralised sequencers that could theoretically censor or reorder transactions. The industry is working toward decentralised sequencing, but users should understand the current trust model of any L2 they use actively.
Tools and Tooling
The tool landscape for DeFi users has improved substantially. Portfolio trackers like DeBank, Zapper, and Zerion provide comprehensive views of positions across chains and protocols. Position monitoring tools alert on liquidation risk, unusual price movements, or protocol-level issues. Tax tools like Koinly and CoinTracker handle the increasingly complex reporting requirements across jurisdictions.
Transaction builders that simulate and optimise complex DeFi operations have become more accessible. DeFi aggregators route swaps and cross-chain transfers optimally across available venues. Intent-based platforms (CoW Swap, 1inch Fusion, UniswapX) provide MEV-protected execution. Using the right tools can meaningfully improve outcomes and reduce costs.
RPC endpoints matter more than many users realise. Public RPCs expose transactions to the public mempool, where MEV bots can sandwich swaps. Private RPC endpoints from providers like Flashbots Protect or MEV Blocker route transactions through private orderflow, providing MEV protection without sacrificing execution quality.
Regulatory Awareness
Regulatory clarity has improved in many jurisdictions through 2025 and 2026, but the landscape remains complex. Users should understand the tax treatment of their activities in their home jurisdiction, keep records of all transactions, and consult professionals for complex situations involving cross-jurisdictional activity or significant capital gains.
KYC requirements on various on-ramps and off-ramps have expanded. Users should be aware of which services require identity verification and how this interacts with their privacy preferences and record-keeping needs. Some purely on-chain activities remain outside current regulatory frameworks in most jurisdictions, but the direction of travel has been toward greater reporting and compliance requirements.
Operational Habits
Beyond technical security, operational habits matter. Using separate wallets for different purposes (a hot wallet for day-to-day activity, a cold wallet for long-term holdings, dedicated wallets for specific protocols) compartmentalises risk. If one wallet is compromised, the others remain unaffected.
Testing new protocols with small amounts before committing meaningful capital is a universal best practice. The user experience of deposit, withdrawal, and interaction can reveal issues that aren't apparent from reading documentation. Small test transactions also verify that the user understands what they're doing before exposing larger amounts.
Keeping some portion of holdings in simple, well-understood positions (major assets, major stablecoins in the most audited venues) provides both a psychological and practical buffer. Complex, high-yield strategies are more rewarding when they succeed but also carry higher risk. Balancing the portfolio between complexity and simplicity suits different user preferences and risk tolerances.
The Core Principles
The underlying principles of DeFi best practice have not really changed: understand what you're interacting with, limit your exposure to what you can afford to lose, diversify across protocols and chains, monitor positions actively, and stay current on evolving threats. The specific tools and techniques have improved, and the threat landscape has evolved, but the fundamental mindset, informed, cautious, and actively engaged, remains the foundation of successful long-term participation in DeFi.
Users who treat DeFi as a serious financial activity, apply the same diligence they would to any significant investment, and continuously update their practices as the ecosystem evolves, tend to outperform those who approach it casually. The rewards are available, but so are the risks, and closing the gap between the two requires ongoing attention and care.
Exploring DeFi via Portals.fi
Portals.fi is a DeFi aggregation platform that allows users to interact with various DeFi protocols through a unified interface. Users can access protocols across multiple chains, compare opportunities, and manage positions from a single access point, supporting the diversification and operational efficiency that best practice recommends.
For more information about how Portals.fi works, visit portals.fi.
This article is for informational purposes only and does not constitute financial advice. DeFi protocols carry inherent risks, including smart contract vulnerabilities, liquidation risk, and market volatility. Always conduct your own research before interacting with any protocol. For our full disclaimer, please visit here.
Portals.fi Blog Newsletter
Join the newsletter to receive the latest updates in your inbox.